The first Linux Security Summit (LSS) was held last Monday, 9th August in Boston, in conjunction with LinuxCon 2010 North America.
This event has its roots in the Linux security development community which emerged in the early 2000s, following the development of LSM and with the incorporation of a wide range of new security features into Linux. We’d previously met, as a community, in OLS BoF sessions, various conference hallway tracks, and at project-specific events such as the SELinux Symposium. There have also been very successful security mini-summits at LCA in 2008 and 2009, and a double security track at the 2009 Plumbers Conference.
This year, we tried to broaden the scope of the event as far as possible — to situate it with a more general Linux conference (than Plumbers, for example), and bring in not only developers, but the wider end-user community as well. We had great attendance from the security developer community, with pretty much all major areas of development represented, although not as many end-users as we’d hoped for. We were, however, easily able to fill up a days worth of bleeding edge technical discussions, with around 70 developers in attendance throughout.
Presentations were limited to thirty minutes, including discussion, to help ensure an interesting and stimulating event, aimed at fostering ongoing discussion and engagement. In this sense, it seems we were generally successful, with several strong discussions arising during presentations. There were many follow-up meetings between developers, end users and vendors during the remainder of LinuxCon, which was very gratifying to see.

Z. Cliffe Schreuders sparking a lively debate about security usability
Mobile security was one of the core issues discussed at LSS (and during the rest of the week), with the year of the Linux desktop now apparently permanently canceled due to smartphones and similar devices. There are certainly many very difficult and exciting challenges to be met in this area over the coming years, and it was great to be able to have the MeeGo security folk present on their work.
Another important area (as always), is security usability, with new high-level policy language work presented by Josh Brindle (lolpolicy). Z. Cliffe Schreuders presented the results of a comparative usability vs. efficacy study from his FBAC-LSM project, sparking some very robust and productive discussion. (Certainly from an SELinux point of view, we are trying to learn as much as possible from this kind of research, which is otherwise very thin on the ground).
Stephen Hemminger presented on the topic of integrating security into a router (Vyatta). This kind of presentation is really very useful to have when there are so many security developers present — it helps us better understand the nature & scope of security requirements for a wider range of real-world users.
Brad Spengler’s presentation addressed the difficult area of protecting the kernel itself, arising from his experiences developing grsecurity. As most of our protection mechanisms operate within the kernel, attacks on the kernel can render these mechanisms useless, so it is important to try and harden the kernel as much as possible. Brad outlined some areas which we still need to address upstream (or in distros, at least), a topic which was further developed by Kees Cook in his talk on Out of Tree security features.
IMHO, we face a number of challenges in this area: 1) core kernel developers are not always receptive to enhanced security, 2) the solutions proposed often are technically not acceptable to upstream (and require a lot of persistent reworking) and 3) we don’t have a huge pool of available expertise upstream in these areas. Kees has taken on some of the challenges here, and any additional contributors here would certainly be welcome, although I would not anticipate any smooth sailing.
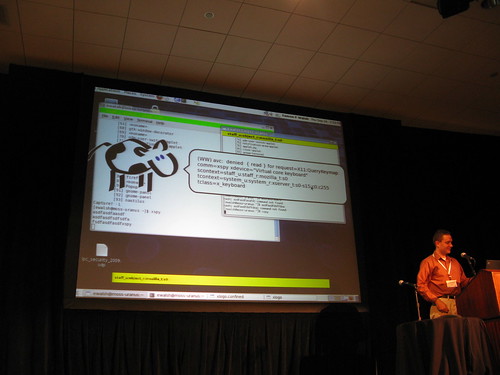
We also had project updates from Mimi Zohar on EVM, Karl MacMillan on security management, Dan Walsh on SELinux Sandbox, and Stephen Gallagher on SSSD.
The panel discussion kicked off with a session on the viability of a standard Linux security API. It was good to get a discussion going here, with well-considered input from key developers. It seems the consensus is that our various security models are too fundamentally different to develop the kinds of APIs you might see in proprietary OSes, although the issues are certainly recognized (e.g. hindered ISV and end user adoption of security) and people are thinking about solutions. There are many difficult, open issues in this area, although we really don’t have the option of not solving them — as a society we’re ever increasingly reliant on computing, and thus also on its security.

Casey Schaufler leading the security API panel discussion
There’s already been quite a lot of feedback from attendees on the format and co-location of future events. There was some talk of aiming at a more purely technical conference (e.g. Plumbers), although it seems to me that there was a great benefit in being able to assemble a critical mass of security developers alongside the other LinuxCon developer mini-summits, as well as general end users, vendors etc. A couple of people also mentioned the Collab summit, although I wonder if being invite-only may limit the overall scope of participation. We may also look at a two-day event next year, to allow for keynotes, a few selected longer talks for major new projects, and break-out sessions.
If anyone has feedback or ideas, please join the LSS mailing list and post your thoughts.
Slides from the presentation are now linked from the schedule (where available), and I’ve posted a brief photo set on flickr. If you post any photos or blogs from the event, please tag them with #lss2010, and drop me an email, so I can link to them from the web site.
Overall, it seems that we had a very productive and collaborative event, bringing together key people to discuss ongoing and emerging challenges in Linux security. Indications thus far are that we should expect to see useful developments arise out of discussions begun at this summit, in some of the areas mentioned above.
The Linux Foundation organizers seamlessly provided us with everything we could need in terms of a venue and support — allowing us to concentrate on the program itself. Many folk worked behind the scenes, but I’d like to especially thank Angela Brown, C. Craig Ross and Amanda McPherson.
Also thanks to everyone who presented and attended, and to the program committee, who worked quickly to review and evaluate all the proposals.