Last week was a busy one in Portland, starting with the SELinux Developer Summit on Sunday the 20th, followed by LinuxCon proper, and the Linux Plumbers Conference.
The SELinux event went very smoothly, with around twenty-five attendees from the core SELinux developer community. Given tight travel budgets all-round, this level of attendance was very good to see. I’d like to thank Angela Brown, Craig Ross and the rest of the Linux Foundation team for making everything work perfectly for us (this was a co-located event ahead of LinuxCon).
The day was divided into two sessions: standard presentations in the morning, followed by a more open general session in the afternoon. It was good to catch up on the latest development work and directions in the project, and also to bring the otherwise globally distributed team together in the same place.
The inaugural LinuxCon then ran for three days, with an expansive programme. I gave a talk on adding extended attribute support to Linux NFSv3 — the slides for which may be downloaded as PDF or viewed on slideshare. I completed the initial code on the flight to the US and posted it from the hotel. Feedback so far has been positive, although I haven’t heard from the NFS maintainers yet (who are likely busy with the merge window). The rationale and technical approach is similar the NFSv3 ACL support which was merged some time ago; and the implementation is based on a fielded IRIX version (released under the GPL) — both factors which I hope will help with upstream acceptance.
Also at LinuxCon: Dan Walsh gave a talk on sVirt, which I introduced earlier this year at LCA (and previewed of during a lightning talk last year at FOSS.MY). It seems to have been well-received (see LWN coverage), and it’s a good example of the high-level security abstractions which we can build once we have the underlying mechanisms in place. In the case of sVirt, where we apply strong mandatory isolation to process-based virtualization (e.g. SELinux+KVM), there is zero configuration — it configures itself automatically depending on which security model you have enabled. It should work with any label security scheme, such as Smack, and I’ve also heard that the AppArmor folk have it working (even though sVirt was not explicitly designed for pathname security).
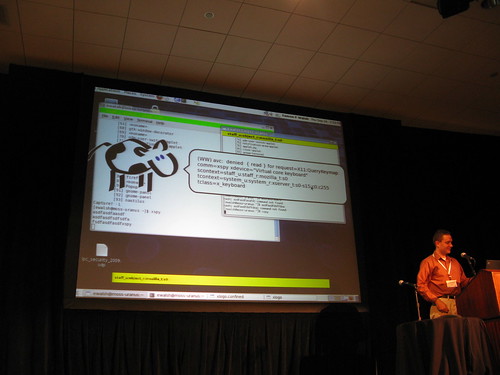
Dan gave a LinuxCon lightning talk at Linux on yet another high-level security feature: Sandbox X, which extends the SELinux sandbox mechanism to the desktop by running applications in isolated X servers via Xephyr. He gave a full talk on this the Linux Plumbers Conference, slides of which may be found here.
I don’t have the time to cover everything at LinuxCon — check the web site for videos and slides. Also see my flickr photo set. It was a very impressive first conference, with LCA-quality social events and catering (Angela Brown has been quietly studying LCA, in fact) and certainly sets a new standard for such events in North America. LinuxCon will be held in Boston next year — I wonder what they’ll come up with to beat bacon-maple donuts for breakfast.
Following LinuxCon, the second Linux Plumbers Conference was held, and we were fortunate to get a double session for the security microconf (a special thanks to Nivedita Singhvi and team for making this possible). We had talks on several Linux security projects, including Herbert Xu with an update on the kernel crypto API, Caleb Case on SELinux in Ubuntu, David Safford on IMA, and Casey Schaufler on the Smack application ecosystem (some high-end televisions will soon be shipping with Smack, to isolate the applications of competing content providers).
The XACE talk was very interesting, as we’re getting close to having workable support for MAC security inside X, which will allow the desktop to be locked down with fine-grained and comprehensive controls. While typically envisaged for MLS use (e.g. having “secret” and “unclassified” desktop applications running on the same system), there are also many general purpose scenarios, such as separating your online banking session from your IRC chats. It will be interesting to see what’s possible when combining XACE window labeling with Sandbox X — stay tuned.
Slides from the LPC microconf will be at the event web site soon, and I’ve also made all them available for download here.
It was a fairly intense week — three conferences plus the travel to and from Sydney, as well as the merge window opening a few days before. I’ve got a few weeks to recover and then it’s Japan for the Kernel Summit and Japan Linux Symposium, stopping in Kuala Lumpur on the way back for FOSS.MY (where I’ll be covering the latest in SELinux Sandboxing).
**
Note that you can now follow my micro-updates on twitter, which is bridged from my identi.ca account.